Cyber Security of Government Networks and Systems

Report metadata
- Tabling date:
- Audited entities:
- Communications Security Establishment Canada
- Shared Services Canada
- Treasury Board of Canada Secretariat
- Report type
- Auditor General reports
At a glance
Overall, we concluded that the federal government had tools in place to protect and defend government networks and systems from cyber threats; however, there were significant gaps in cyber security services, monitoring, and response during active attacks. As cyber attacks become more sophisticated, pervasive, and harmful, the federal government must continually bolster its defences.
The responsibility for protecting government information technology (IT) systems and operations is shared by the Treasury Board of Canada Secretariat, Communications Security Establishment Canada, and Shared Services Canada. The organizations work together and with departments and agencies to prevent data theft and limit disruptions to systems that deliver programs and services to Canadians. However, not all federal organizations were subject to the same security policies, which resulted in the inconsistent use of available cyber security services. Gaps in cyber security defences undermine the government’s ability to protect critical information and manage cyber security risks.
Protecting federal networks and systems also requires the government to analyze the potential vulnerabilities of all government devices, including laptops, smartphones, and servers. Our audit found that Shared Services Canada and Communications Security Establishment Canada did not have a comprehensive, up-to-date inventory of all government IT assets. In 2017, Shared Services Canada began developing a cyber security project designed to provide a complete view of government devices, but the project had not been completed. Without up-to-date IT information across all departments and agencies, the federal government risks not being aware of—let alone being able to quickly respond to—changing cyber security challenges.
We also found that the coordination among the 3 organizations was insufficient during active attacks. For example, a lack of information sharing delayed the government’s response to a significant cyber attack in January 2024, allowing the attacker prolonged access to personal information. At the time of our audit, an initiative to set up a cyber security collaboration platform and incident case management tool had not received funding.
Key facts and findings
- From April 2023 through March 2024, Communications Security Establishment Canada’s network-based sensors blocked about 2.4 trillion suspicious cyber security events, which ranged from simple network scans to sophisticated cyber attacks.
- From October 2023 through September 2024, Shared Services Canada’s secure Enterprise Internet Service blocked about 6.6 trillion suspicious cyber security events.
- In June 2024, Shared Services Canada put the Security Information and Event Management project on hold. This initiative aimed to identify suspicious cyber security events and trigger automated responses to cyber attacks if detected.
- Budget 2024 provided the Treasury Board of Canada Secretariat $11.1 million over 3 years to lead the implementation of a cyber security strategy. We found this strategy, launched in May 2024, to be sound and comprehensive.
Why we did this audit
- As cyber attacks become more sophisticated, frequent, and damaging, the federal government’s defences must continually evolve to successfully protect its networks and systems, including sensitive information and Canadians’ personal information stored within them.
- Having a sound and comprehensive cyber security strategy focusing on the federal government is important for managing cyber security risks.
- Gaps in the cyber security of government networks and systems as well as delays in responding to cyber attacks increase the likelihood that these cyber attacks may succeed, resulting in the theft of personal or sensitive information and in damage to IT systems. In turn, this can affect the delivery of programs and services to Canadians.
Highlights of our recommendations
- Shared Services Canada, in collaboration with Communications Security Establishment Canada, should develop a clear action plan with defined criteria and a timeline to develop a Security Information and Event Management application that addresses the existing gaps in cyber security monitoring.
- Shared Services Canada should ensure that it has an up‑to‑date central inventory of networks and systems across federal organizations it services and a process to manage devices that need to be patched, updated, maintained, or replaced.
- The Treasury Board of Canada Secretariat, Communications Security Establishment Canada, and Shared Services Canada should re‑evaluate their cyber security incident management practices to enable the better coordination and timely sharing of required critical information when responding to cyber attacks affecting federal organizations.
Exhibit highlights
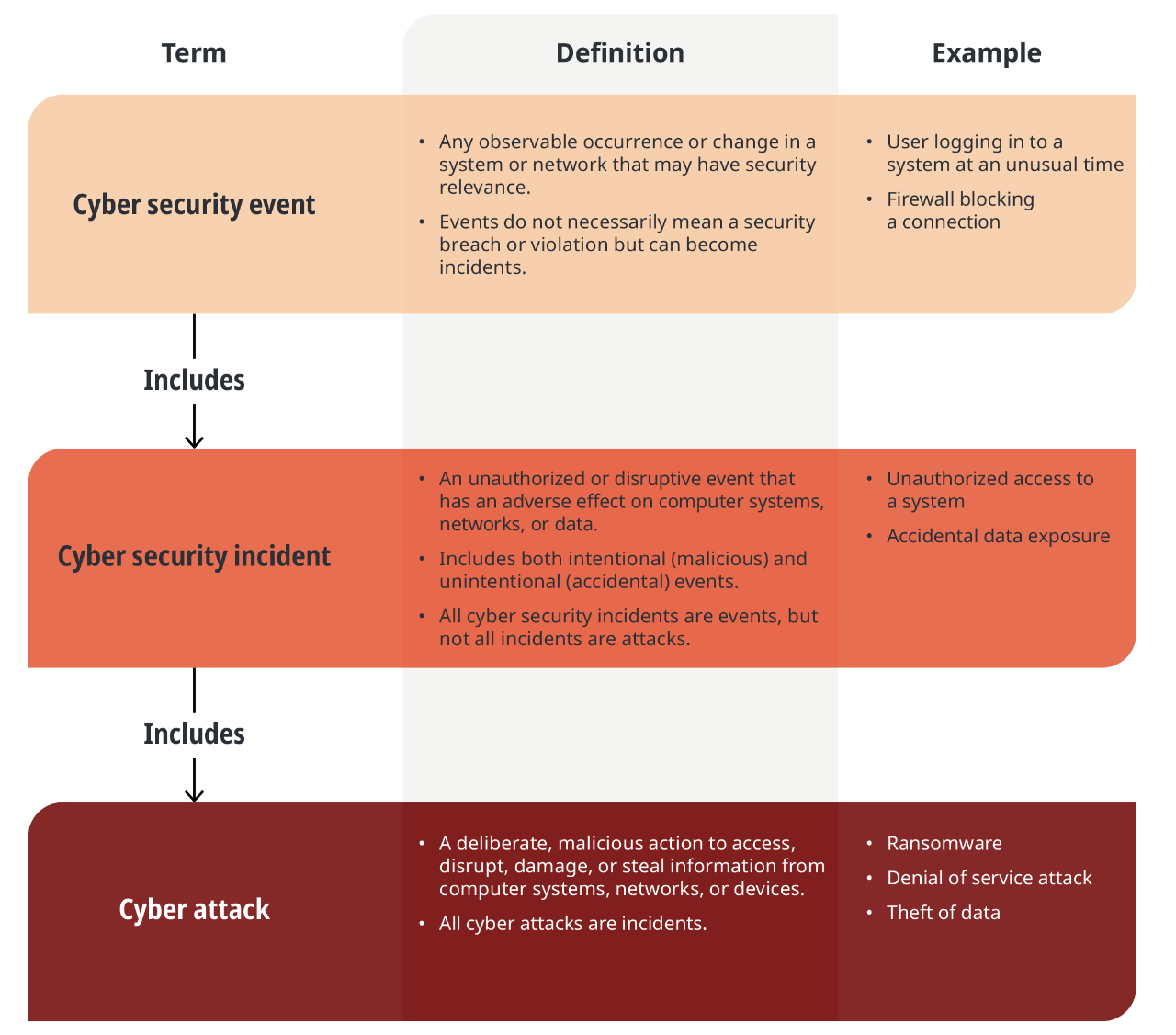
Cyber security event, cyber security incident, and cyber attack
Text version
This chart defines the terms “cyber security event,” “cyber security incident,” and “cyber attack” and includes examples for each term. It also shows that a cyber security event includes a cyber security incident and that a cyber security incident includes a cyber attack.
A cyber security event is any observable occurrence or change in a system or network that may have security relevance. Events do not necessarily mean a security breach or violation but can become incidents. Two examples of cyber security events are as follows:
- a user logging in to a system at an unusual time
- a firewall blocking a connection
A cyber security incident is an unauthorized or disruptive event that has an adverse effect on computer systems, networks, or data. It includes both intentional (malicious) and unintentional (accidental) events. All cyber security incidents are events, but not all incidents are attacks. Two examples of cyber security incidents are as follows:
- an unauthorized access to a system
- an accidental data exposure
A cyber attack is a deliberate, malicious action to access, disrupt, damage, or steal information from computer systems, networks, or devices. All cyber attacks are incidents. Three examples of cyber attacks are as follows:
- ransomware
- a denial‑of‑service attack
- a theft of data
Objectives and key actions of the Government of Canada Enterprise Cyber Security Strategy

Text version
This chart shows the strategy objectives and examples of key actions of the Government of Canada Enterprise Cyber Security Strategy.
The strategy’s vision is as follows: “Building a world‑class, sustainable, and resilient federal government to reduce cyber security risks so that departments and agencies can enable secure and reliable digital service delivery.” The federal organizations that are responsible for implementing the strategy are the Treasury Board of Canada Secretariat, Communications Security Establishment Canada, Shared Services Canada, and other departments and agencies.
The chart lists 4 strategy objectives, and 2 examples of key actions are listed for each objective. There are many other actions under the strategy. The examples listed here represent some of the actions intended to have a government‑wide impact.
- Strategy objective: Articulate cyber security risk and its business impacts. The 2 examples of key actions are as follows:
- Establish a government‑wide compliance and assurance program to assess departments’ cyber security defences to identify and prioritize cyber security risks.
- Create a government‑wide vulnerability management program to manage and reduce vulnerabilities affecting government systems and networks.
- Strategy objective: Prevent and resist cyber attacks more effectively. The 2 examples of key actions are as follows:
- Expand cyber security defences to small departments and agencies.
- Establish a framework to improve the ability to detect and prevent fraudulent activity against government applications.
- Strategy objective: Strengthen capabilities and resilience across the Government of Canada. The 2 examples of key actions are as follows:
- Establish a framework for departments to maintain accurate asset inventories of government applications and systems. Conduct year‑round testing and reviews of cyber security protection and defence.
- Implement a government‑wide cyber security event collaboration platform to manage and respond to cyber events.
- Strategy objective: Foster a diverse federal workforce with the right cyber security skills. The 2 examples of key actions are as follows:
- Build cyber talent through cross‑functional training programs in cyber security.
- Promote a talent management culture to recruit and retain skilled candidates.
Communications Security Establishment Canada developed 3 types of cyber security defence sensors to detect and mitigate cyber security events and cyber attacks

Text version
This chart shows the 3 types of cyber security defence sensors that Communications Security Establishment Canada developed and the years when they were each deployed.
In 2010, the department deployed the network‑based sensor, which detects and mitigates cyber security incidents on the government’s networks. This sensor is typically integrated with Shared Services Canada’s Enterprise Internet Service.
In 2012, the department deployed the host‑based sensor, which detects cyber attacks on IT endpoint devices such as laptop computers, servers, and local networks. The sensor analyzes and processes collected information to detect suspicious cyber security events occurring on a host machine. The information gathered is used to report anomalies and weaknesses to affected federal organizations.
In 2019, the department deployed the cloud‑based sensor, which operates in federal organizations’ cloud infrastructure and works in conjunction with the defences provided by cloud vendors. This sensor automates the collection of logged activity in the cloud and analyzes the information to detect and mitigate suspicious cyber security events.
The 119 federal organizations not required to use the cyber security services of Shared Services Canada (SSC) and Communications Security Establishment Canada (CSE) were encouraged to use the services, but many chose not to

Text version
This exhibit presents 2 charts: 1 chart showing the number of federal organizations that voluntarily use Shared Services Canada’s Enterprise Internet Service and 1 chart showing the number of federal organizations that voluntarily use Communications Security Establishment Canada’s cyber security defence sensors.
Of the 119 federal organizations that are not required to use Shared Services Canada’s Enterprise Internet Service, 24 organizations, or 20%, voluntarily used it, and 95, or 80%, did not.
Similarly, of these 119 organizations, 76 organizations, or 64%, voluntarily used 1 or more of Communications Security Establishment Canada’s cyber security defence sensors, and 43, or 36%, did not.
Infographics
Infographic 1

Text version
Shared Services Canada's Enterprise Internet Service blocked trillions of cyber threats.
There were 6.6 trillion threats blocked in just 12 months, including attacks, malicious actions, and external events.
That’s averaging 18 billion attempts a day.
Infographic 2

Text version
Not all organizations are using Shared Services Canada’s and Communications Security Establishment Canada’s cyber security tools.
Out of 204 federal organizations, 119 organizations are not required to use the enterprise service. Twenty‑four of these organizations have adopted this service to provide security from malicious sites. That’s 20%.
The remaining 85 organizations are required to use Shared Services Canada’s Enterprise Internet Service for security, site filtering, and Communications Security Establishment Canada monitoring. Only 63 of these organizations were using this required service.
Infographic 3
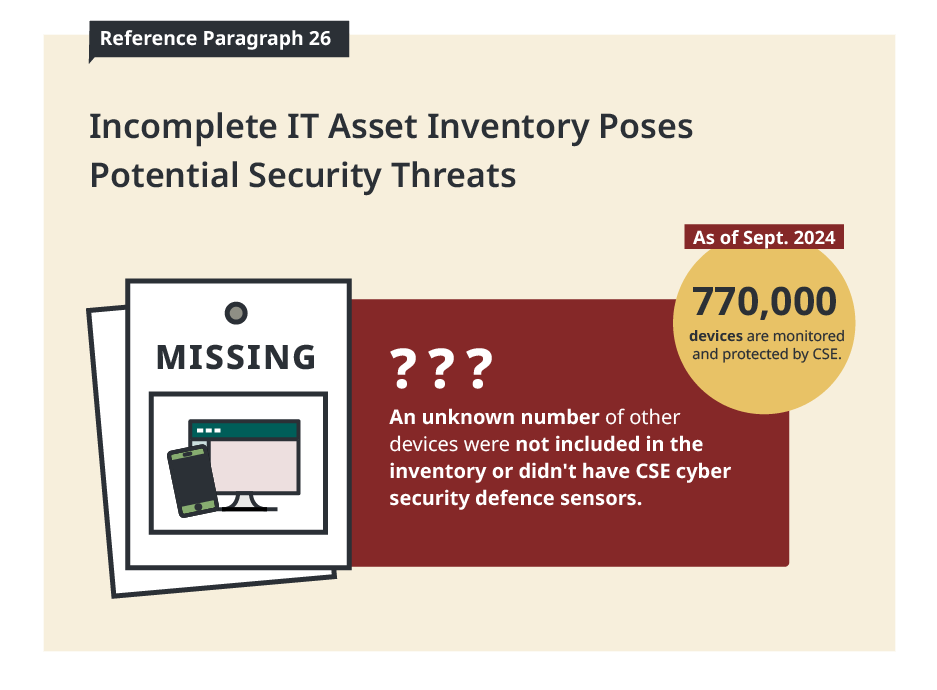
Text version
Incomplete information technology asset inventory poses potential security threats.
As of September 2024, 770,000 devices are monitored and protected by Communications Security Establishment Canada.
An unknown number of other devices were not included in the inventory or didn't have Communications Security Establishment Canada cyber security defence sensors.